eva
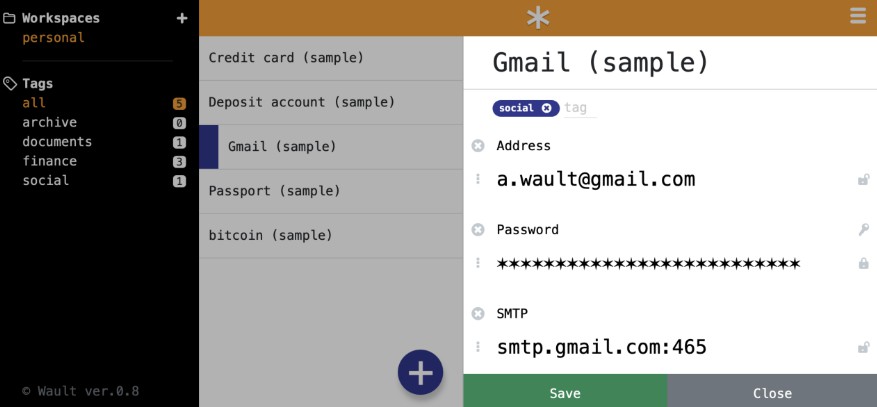
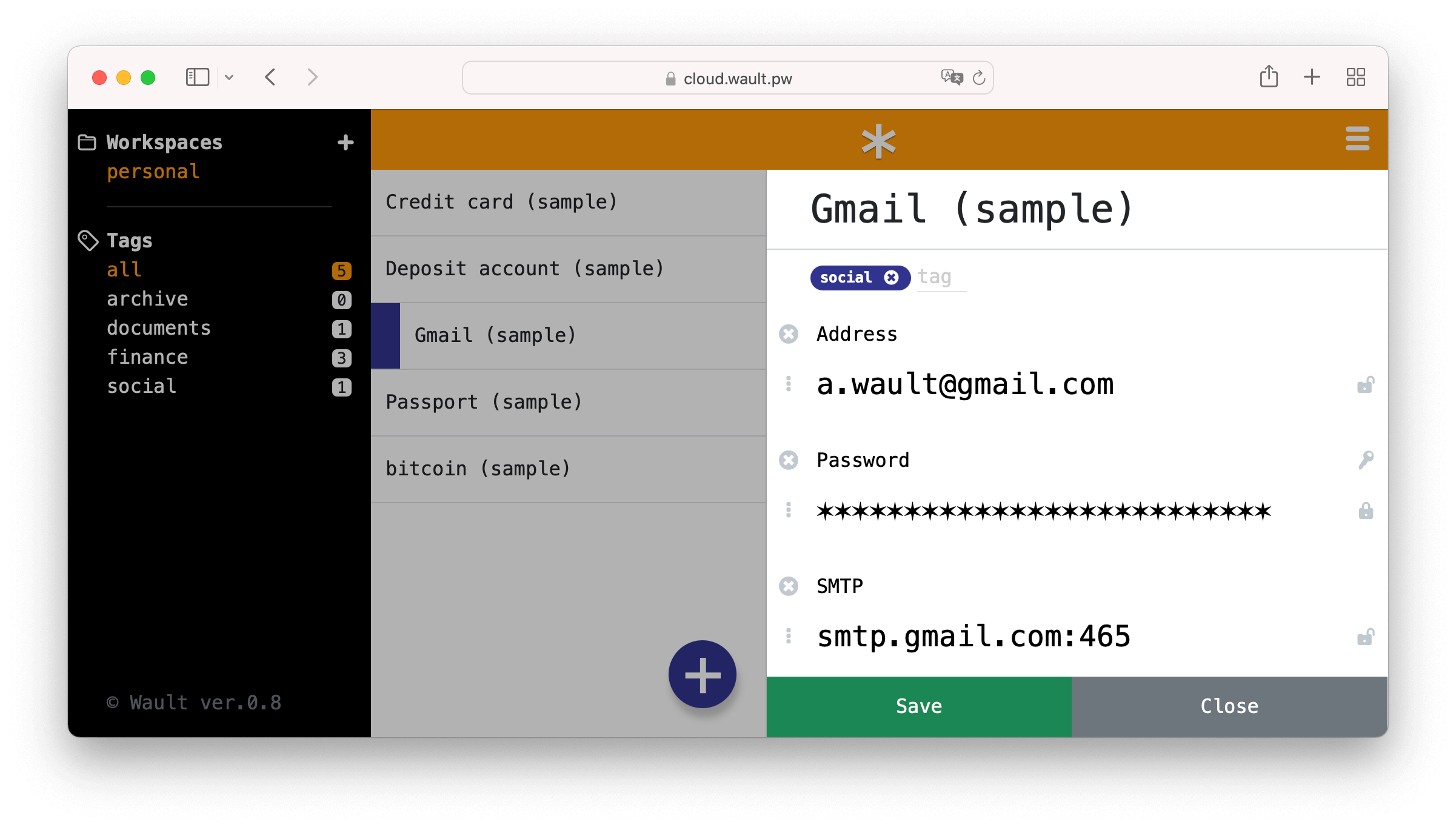
To avoid storing data on the server, the Wault password manager encrypts and decrypts data inside the browser. The keys for all encryption processes are derived from the password, which is never sent to the server.
In simple terms, Wault password manager is an online service that knows nothing about its users. Wault looks like an ordinary web application, but hides a powerful cryptographic mechanism entirely created and executed in your browser.
Based on this idea, we developed and implemented a web application architecture that supports your privacy. The main idea was to create a trust-free service, where users could trust the data within the browser, regardless of external sources.
Docker setup
The simplest docker installation
(implies you are using local Postgres), looking the following. First, you should create an
empty database psql -c 'CREATE DATABASE alice'.
docker run --rm -e PG_DSN="postgres://[email protected]:5432/alice?sslmode=disable&timezone=utc" -p 3000:3000 shlima/wault
Production ready setup should be like this one. Please provide your own random keys.
SSE_KEYfor server side encryptionJWT_KEYfor signing JWT cookiesCOOKIE_SECUREset totrueif you run wault instance behind the HTTPSCOOKIE_DOMAINset a domain name if you run wault instance within your domainALLOW_ORIGINset the origin if you run wault instance on a port other than3000,
or within your own domain name, example:http://localhost:8080orhttps://wault.local
docker run --rm \
-e PG_DSN="postgres://[email protected]:5432/alice?sslmode=disable&timezone=utc" \
-e SSE_KEY=bf02ee811878d6cd9eebb823e54d2bdc318b4fc676df9c3f709f8c9c6ca8fff0 \
-e JWT_KEY=7cfa6c528a3060810ae8337382b99a9eaaf305a8055d4739df8312155a0d93d8 \
-e COOKIE_SECURE=false \
-e LOCALE=en \
-e PRODUCTION=true \
-p 3000:3000 \
shlima/wault